One of the most common points of confusion I see in the compliance space is the conflation of a compliance risk assessment and a fraud risk assessment. At first glance, they may look similar as both touch on governance, controls, and organizational exposure. Yet, as Jonathan Marks emphasized in a recent episode of the Data-Driven Compliance podcast, they are not the same. They serve different purposes, employ different methodologies, and generate different impacts. And if you blur the two, you may be leaving the corporate back door wide open.
In this post, I aim to explore the distinctions, explain why they matter, and demonstrate how both assessments complement one another in building a stronger, more resilient compliance program.
Compliance Risk Assessment: Coloring Inside the Lines
A compliance risk assessment is the backbone of the compliance function. It answers the question: Are we following the laws, regulations, and internal policies to which we are required to adhere?
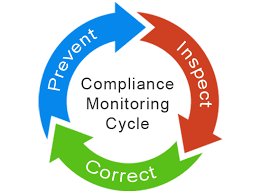
The methodology is structured around:
- Identifying obligations — What laws, regulations, and internal codes apply to our business?
- Assessing exposure — Where are we most likely to be out of compliance?
- Evaluating controls — What policies, procedures, and safeguards exist to manage those obligations?
- Prioritizing remediation — Which gaps carry the greatest legal, financial, or reputational risk?
The Department of Justice (DOJ) has long framed this as a “three-question test”: Is your program well designed? Is it implemented in good faith? Does it work in practice? A compliance risk assessment is the diagnostic tool that helps answer these questions.
Consider this: a compliance risk assessment ensures that the organization operates within the bounds of the law. It helps the business avoid the unintentional missteps that could land it in hot water with regulators.
Fraud Risk Assessment: Thinking Like a Fraudster
By contrast, a fraud risk assessment is not about whether you are following the rules; it is about whether someone could deliberately break them, deceive the organization, and benefit at its expense. Marks put it succinctly: compliance without fraud detection is like locking the front door while leaving the back door wide open.
A fraud risk assessment is built around three key elements:
- The Act – The fraud scheme itself. Examples include false vendor setups, revenue inflation, insider collusion, or misuse of restricted funds.
- The Concealment – How the scheme is hidden. Fraud is rarely obvious. It may involve falsifying documents, manipulating data, overriding controls, or exploiting process weaknesses.
- The Conversion – How the perpetrator benefits. Whether through cash, bonuses, promotions, or reputational gain, there is always a payoff.
This approach is fundamentally about mindset. A compliance risk assessment looks at processes. A fraud risk assessment forces you to think like the fraudster, the “mind behind the crime.”
Methodological Differences
Marks emphasized that while compliance risk assessments and fraud risk assessments may overlap, their methodologies diverge in several important ways:
- Focus on Intent vs. Process
- Compliance asks: Are we following the rules?
- Fraud asks: Could someone intentionally subvert the rules, and would we detect it in time?
- Scope of Risk
- Compliance focuses on legal and regulatory exposure.
- Fraud encompasses a broader range of threats, including financial, operational, and reputational risks—whether driven by insiders or outsiders.
- Tools and Techniques
- Compliance assessments often rely on surveys, documentation review, and structured interviews.
- Fraud assessments utilize forensic tools, including analytics, behavioral red flags, and targeted scenario testing, to identify potential risks.
- Outcomes
- Compliance assessments typically produce policies, certifications, and gap analyses.
- Fraud assessments deliver actionable detection and deterrence strategies.
Red Flags: The Early Warning System
One of the most practical contributions of a fraud risk assessment is its focus on red flags, the early warning signs that something is not right. Marks categorized them into four groups:
- Data Red Flags – Unusual transaction timing, frequency, or amounts.
- Document Red Flags – Missing or altered records, incomplete approvals.
- Control Red Flags – Inadequate segregation of duties, override of established processes.
- Behavioral Red Flags – Employees living beyond their means or facing personal stressors.
The key is not simply to identify these red flags, but to connect them back to your control environment. Are your controls designed to catch intentional deception or only unintentional error? Too often, organizations rely on compliance-oriented controls that were never built to stop someone determined to cheat the system.
Skills and Experience Matter
Another critical difference lies in who conducts the assessment. Compliance risk assessments often require individuals with expertise in law or regulation. Fraud risk assessments, however, require a different skill set; professionals who understand fraud schemes, internal controls, and forensic techniques are needed.
As Marks bluntly put it: certifications are nice, but experience is essential. Those leading fraud risk assessments need to have “skinned their knees” in real-world situations to understand the difference between a red flag and a false signal. Without that expertise, organizations risk a paper exercise that fails to capture the real threats.
Complementary, Not Substitutes
It is tempting for organizations to assume that a compliance risk assessment also covers fraud risk. That is a dangerous misconception. While the two assessments intersect, they are not substitutes. A compliance risk assessment confirms the rules are being followed—a fraud risk assessment tests whether someone could and would intentionally break those rules for personal gain.
Together, they create a multidimensional view of risk:
- Compliance risk assessments keep the organization lawful.
- Fraud risk assessments keep the organization safe.
When aligned, they reinforce one another. For example, fraud red flags can be embedded into compliance training, transforming static learning into practical, scenario-based awareness. Compliance findings can inform fraud detection by highlighting areas where processes are weakest.
Beyond Reports: Building Organizational Resilience
The ultimate value of both types of assessments lies not in the reports they generate but in the resilience they build. Marks is right to stress that neither should be treated as a “set it and forget it” project. Both are living, breathing processes that evolve in tandem with your business model, regulatory landscape, and risk environment.
A well-executed fraud risk assessment provides a strategic roadmap for preventing, deterring, and detecting fraud early. A well-executed compliance risk assessment ensures that your program is not only designed and implemented but also functioning effectively in practice. Together, they enhance oversight, foster continuous improvement, and promote a culture of integrity.
Final Thoughts
The compliance community is rightly focused on regulatory risk, ensuring that policies, procedures, and obligations are met. But stopping there creates a blind spot. Fraud is intentional, adaptive, and motivated by gain. It exploits weaknesses not only in processes but in culture.
The lesson for compliance professionals is clear:
- Do not assume that your compliance risk assessment covers fraud risk.
- Invest in both assessments, recognizing their differences and complementary strengths.
- Ensure the right people, with the right experience, are conducting each.
- Embed fraud red flags into your training and compliance processes.
At the end of the day, compliance keeps you lawful. Fraud risk management keeps you safe. Organizations that appreciate the distinction and act accordingly will be better prepared to withstand the unexpected, protect their stakeholders, and build lasting trust.